In 2025 the size of the digital advertising market was estimated at $488.4 billion. At the same time, more than $35 billion of the ad budgets were lost due to ad fraud.
It represents 10% of the global ad market size making ad fraud one of the most expensive problems for advertising.
That’s why it’s extremely important for Ad Tech companies to tackle the problem right now to protect their ad campaigns, and hence ad budgets, from fraudsters. MindK, as a company that develops ad tech solutions for marketers and advertisers, always warns our clients about the existing risks and takes actions to make the solution as secure as possible.
To fully understand the problem and develop a working action plan to prevent fraud, let’s dive deeper and find out:
- how big is ad fraud
- what are common and emerging ad fraud techniques
- which ad sectors are most vulnerable and why
- what are the ad fraud detection and prevention methods
How big is ad fraud and its consequences?
We made an overview of the whole ad tech industry and mentioned that one of the main challenges in this business is transparency. The advertiser wants a clear picture of where the ad is placed and where, in the ad tech chain, the money is spent. Lack of this data makes the media budget uncontrolled and prevents a company from making well-grounded decisions.
Here at MindK, we also dealt with a lack of transparency in the advertising industry. One of our projects was dedicated to making processing log-level data clear and transparent. Our client buys airtime from hundreds of radio stations and TV channels and receives a copy of the log to determine what actually aired in different formats, which are very hard to analyze. We helped them develop intelligent software that recognizes different formats and standardizes raw log-level data making the analysis of results easy and transparent.
The transparency challenge is also becoming more complicated because of ad fraud. Advertising works effectively if it is seen and clicked by real people, not bots that simulate human behavior. Bots and other types of ad fraudulent activities are mostly focused on generating false traffic or false interactions with any kind of digital asset in order to earn money.
The size of the ad fraud problem in advertising is really huge. Statistics about wastage due to fraud vary considerably. Some research, for example, a global economic study by Cheq, revealed that losses due to ad fraud reached $35 billion in 2020. At the same time, Statista estimates that losses will reach from $52 billion in 2020 to $100 billion up to 2023.
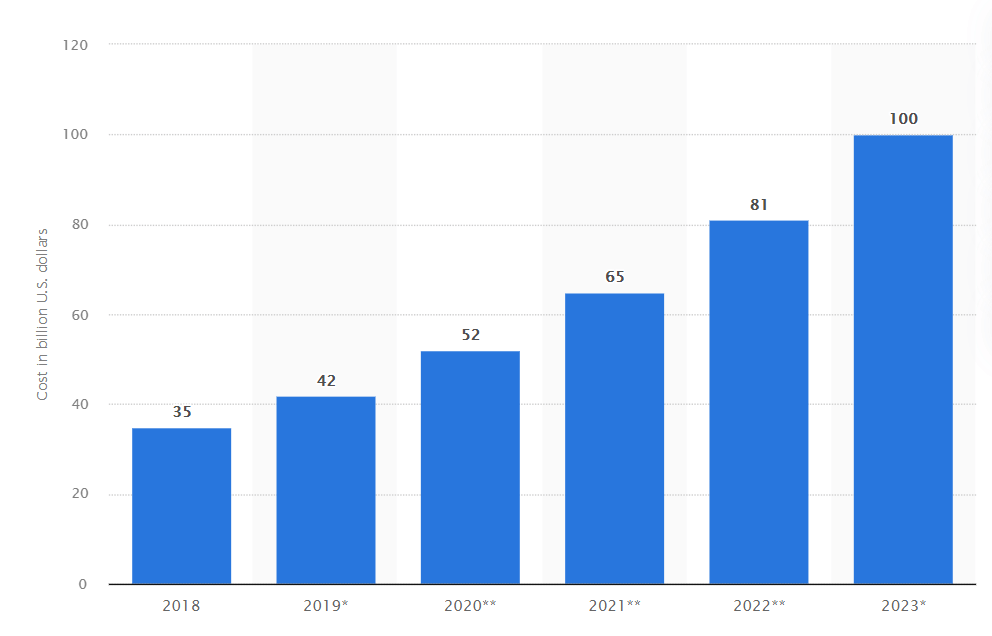
Source: statista.com
There are two main reasons for such discrepancies. First, most tech companies and vendors don’t want to share this data even for research purposes. That’s why companies such as eMarketer, Cheq, White Ops, and others very often have an incomplete picture and disparate numbers when referring to ad fraud losses.
Second, there is no one effective and exact method to determine whether an ad impression is original or not. Almost all the methodologies that companies use to detect ad fraud are not 100% accurate, mostly because of fast-changing fraud and scam tactics. In a nutshell, most reports and research are more assumptions than an accurate picture of what actually happens with ad fraud.
The one thing all researchers strongly agree on is that the ad fraud techniques and methodologies are evolving and becoming more sophisticated, which may result in even more harm for advertisers.
In order to properly evaluate one of the biggest threats of the AdTech industry, companies should consider not only direct but also indirect consequences of fraud. The direct consequence is, for sure, the loss of a good portion of the advertising budget. However, indirect results may be even more dangerous as in the long term, ad fraud negatively impacts:
- marketing decisions;
- budget allocation;
- measurement metrics;
- audience targeting;
- buyer behavior;
- company image; and
- overall lack of trust.
Before we move to the methods to detect and prevent ad fraud, it is recommended to “know your enemy”. It means that it is crucial to understand what are different types of ad fraud and how ad fraud works. This knowledge may help you to fight or even eliminate the ever-growing threat of ad fraud.
Which ad fraud schemes can harm advertising campaigns?
Ad fraud is often referred to as invalid traffic (or simply IVT) that is represented by faking up online ad impressions, clicks, conversions, or other events in order to generate revenue.
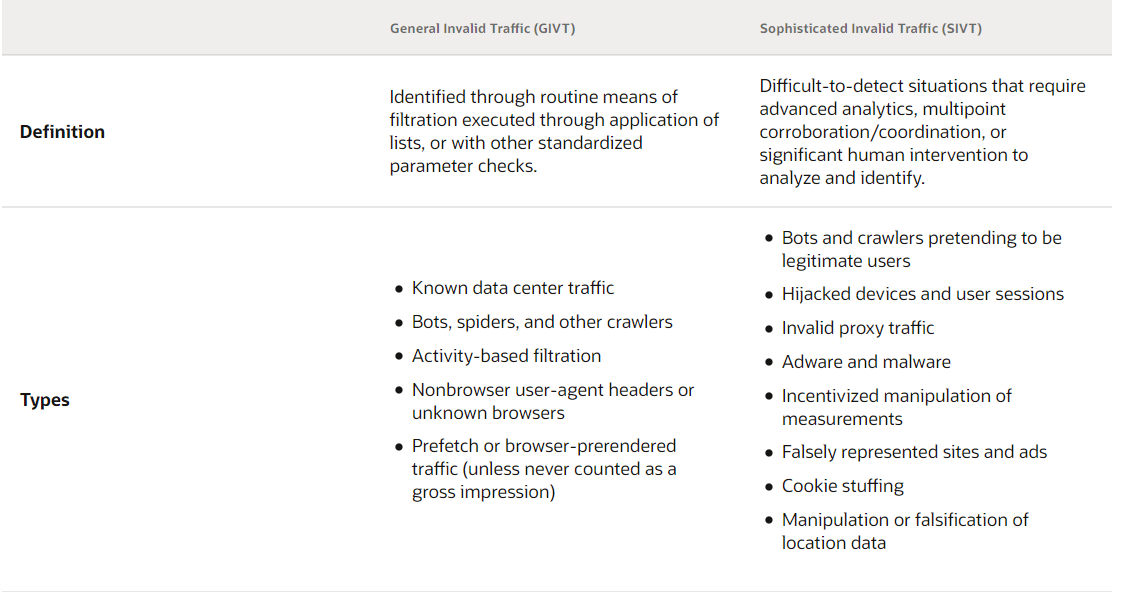
Due to this, it is very important to understand the difference between basic or general invalid traffic and complex or sophisticated invalid traffic and how each type can affect ad campaigns.
Types of the invalid traffic in advertising
Source: oracle.com
General invalid traffic (GIVT) can be compared with background noise. It can take place during ad campaigns but is mostly considered not to be a threat. In general, it’s automatic traffic that is generated by crawlers, legitimate bots, proxy traffic coming through virtual private networks (VPN), and much more that doesn’t simulate human behavior. This makes it relatively easy to detect.
However, such invalid traffic is not 100% harmless. For example, it can result in traffic spikes not caused by real users that can mess up audience measurement data. General invalid traffic involves:
- search robots;
- analytical robots;
- bots of data centers;
- traffic from unknown browsers (for example, using a VPN);
- pre-rendered traffic and so on.
GIVT can be detected using standard list filtering or parameter validation.
Sophisticated invalid traffic (SIVT) is much more difficult to deal with and is what people usually mean when they talk about ad fraud.
SIVT is traffic that allows creating fake views or clicks to generate more revenue. Fraudsters generate SIVT in a variety of ways: domain spoofing, device hijacking, cookie stuffing, and similar. This type of traffic is hard to detect because it simulates human behavior and doesn’t catch the eye. Detecting SIVT requires deep analytics, a reliable tech vendor with good experience in the sphere. The most common SIVT include:
- Malicious bots, robots, and crawlers programmed to intentionally generate fraudulent activities like viewing ads, watching videos, clicking ads, and so on. This type of ad fraud is hard to identify because bots simulate user activity.
- Domain spoofing is when the fraudsters pass off low-quality inventory as high-quality ones. In this way, buyers think their ads are running on a premium site when in reality the ads go to a low-quality website. Although both the inventory and impressions are real, they are purchased at a much higher cost. There is simple domain spoofing that involves URL substitution and cross-domain embedding, and more complex domain spoofing that is based on using custom browsers and malware.

Source: blog.optickssecurity.com
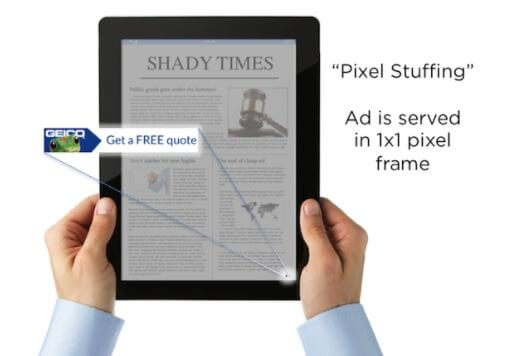
- Pixel stuffing is placing the advertising in one single pixel frame, which makes the ads invisible to the naked eye.
Source: researchgate.net
- Cooking stuffing, also called cookie dropping, is an ad fraud scheme that is based on loading a user’s browser with several third-party cookies in order to generate commission out of sales that happen from that browser. Cookies are “stuffed” into a browser by means of pop-us, iframes, JavaScript or CSS stylesheets. It’s a widespread type of ad fraud in affiliate marketing.
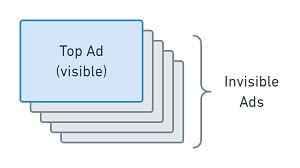
- Ad stacking means displaying a number of ads on top of each other. In such a way only the top advertising banner is seen by the users, while the advertiser pays for impressions even if the person doesn’t see the ad.
Example of ad stacking
Source: comolho.com
- Location fraud happens when the user’s actual location does not match the geotargeting. In this case, the fraudsters send false location information so the ad actually serves in a region different from the one the advertiser needs.
- User-agent spoofing involves modifying the user agent data like browser name, its version, operating system, device type, and similar in order to obfuscate details of the browser or traffic.
- Malicious apps include solutions that generate fraudulent traffic, clicks or impressions without the user knowing about it.
- Hijacking is taking control of a legitimate user’s device/session without their knowledge or consent.
To sum up, the volume of general invalid traffic is often insignificant, while the sophisticated one poses a real threat both for advertisers and publishers. However, there are sectors that are more sensitive to ad fraud than others.
Which ad sectors are the most vulnerable and why?
The majority of ad fraud techniques have been developed on web browsers. Since then, the ad market has worked out a number of standards and protocols to detect and fight fraudulent activities, the majority of ad fraud shifted focus to other platforms, namely, Connected TV (CTV) and mobile apps.
There is no surprise in that. When we made an overview of CTV and OTT advertising, we found out that the number of CTV viewers significantly increased in the last few years. The AdSupply Trends Report by Pixalate states that in 2020 around 72% of US households became reachable by programmatic CTV compared to 50% in 2019.
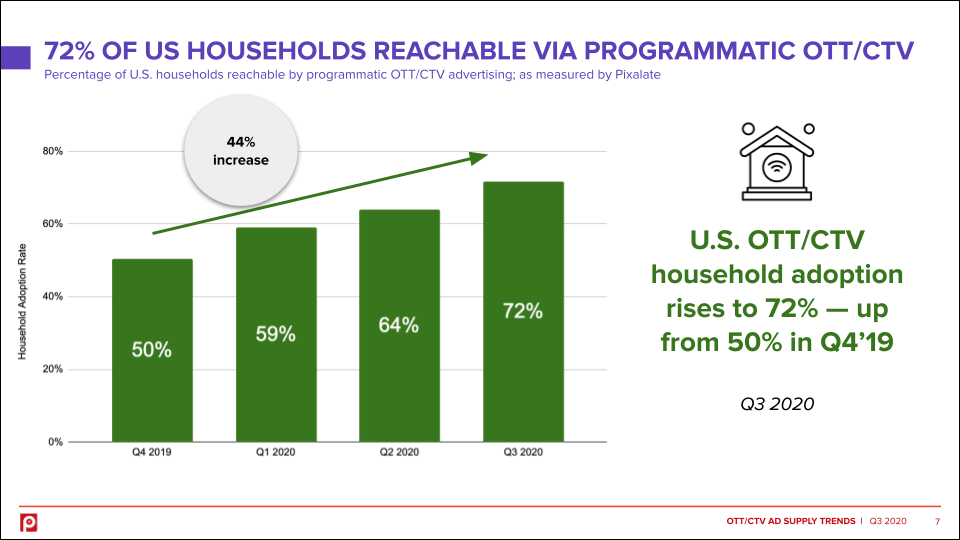
Source: pixalate.com
It is also reported that around 44% of consumers began to spend more time on CTV devices since the COVID-pandemic. In addition to the fact that the popularity of connected TV advertising is growing like a weed, video ads are also one of the most expensive ad formats.
Because fraudsters always follow the money, the sector of connected TV with its higher cost of 1,000 impressions (called cost per mille or simply CPM) is a promising source for them to steal a good slice of the pie from the advertising budgets. We already see it in practice – CTV fraud impressions increased 220% in 2020 compared to 2019 and this trend won’t decline in the near future.
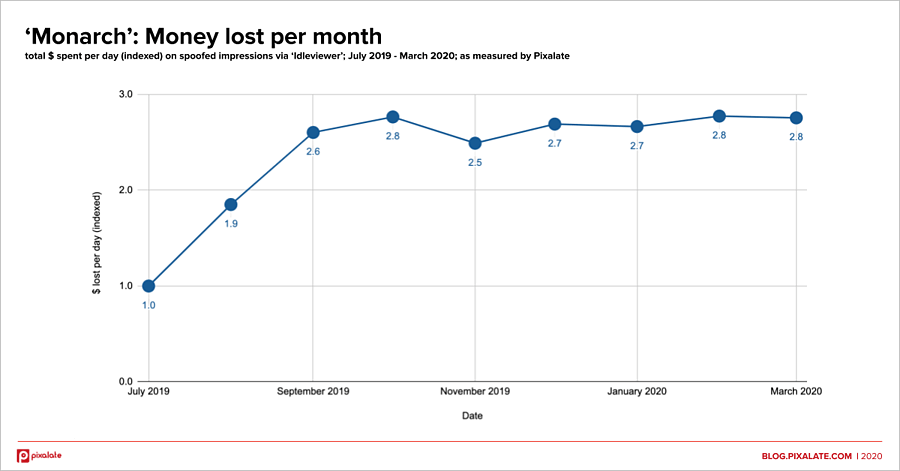
Analyzing the largest ad fraud schemes of 2020 published by Forbes, you’ll see that more than 30% of all the ad fraud schemes are related to CTV ad fraud. All of them turned out to be very expensive for the advertising industry. For example, one of the CTV fraud schemes, Monarch, involved spoofing or misrepresentation of inventory causing millions of dollars in losses.
DoubleVerify claims that the majority of CTV ad fraud schemes go through three phases:
- gathering either IP addresses or app bundle IDs;
- copying this data to mask their activity to protect themselves from being detected; and
- using spoofed details of real users to send fraudulent ad requests.
The company also declared that ad fraud mostly consists of bots on servers and influences a range of inventory. Moreover, fraudsters are instantly learning how to improve their technology, which means paying great attention to ad prevention practices is a must for the advertising industry right now.
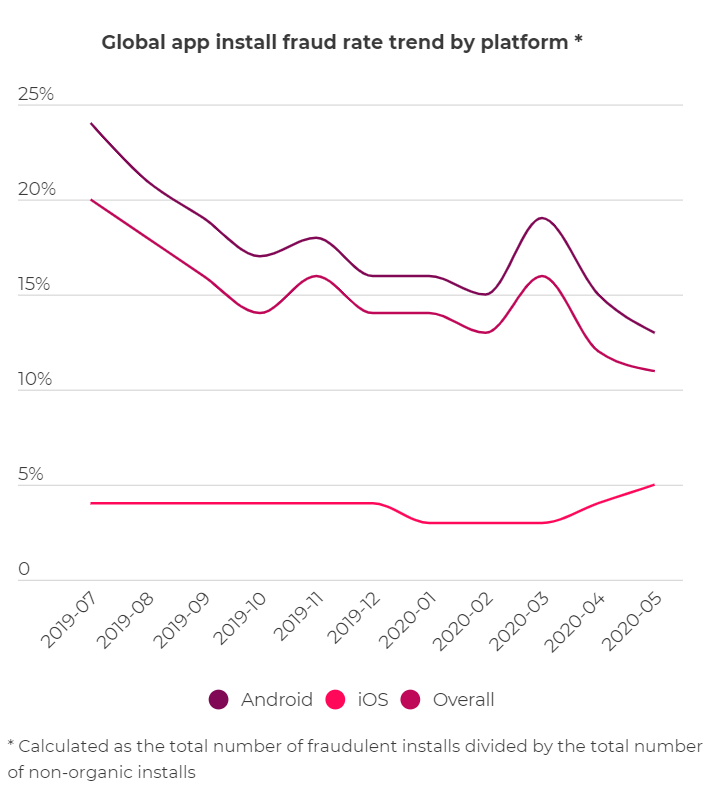
The situation with ad fraud in mobile is also unfavorable. While desktop bots operate by means of malware, app fraud is powered by downloads even from such trusted marketplaces like Play Market or App Store. In 2020 Google removed more than 600 Android apps and banned the developers of these apps from accessing the Play Market as a stern measure against ad fraud and malicious mobile ads.
Android has a large market share worldwide, which is why fraudsters often choose this platform. According to an ad fraud report by Appsflyer, the level of fraud in mobile apps on Android is more than 4.5 times higher than on iOS.
Source: appsflyer.com
It is important to remember that the iOS ad ecosystem is a honey bun for ad fraudsters due to much higher CPMs than Android devices, so there’s a strong possibility that future fraudsters will find a way into the iOS ecosystem.
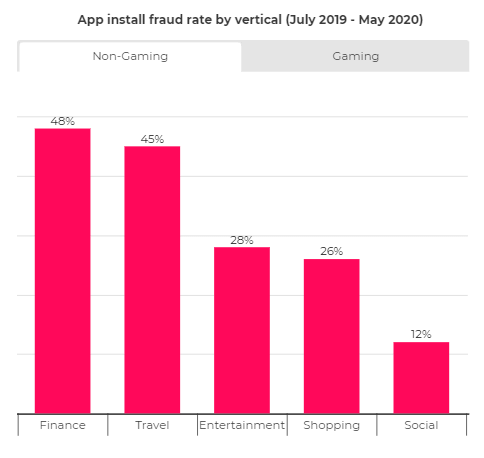
The same report by Appsflyer states that among non-gaming app installations, 32% are fake. Financial apps have the highest fraud rate, followed by travel and entertainment apps. The main source of ad fraud in non-gaming apps is bots that are very hard to detect.
The great need for video and mobile advertising requires urgent solutions and techniques to protect ad budgets from fraud and is, therefore, a brilliant opportunity for Ad Tech companies ready to suggest such products. For example, in September 2021 Pixalate, a real-time fraud protection provider, raised more than $18 million in growth capital to improve its fraud protection platform for connected television and mobile advertising.
How to prevent ad fraud: measures companies take to protect themselves
Although ad fraud is among the top challenges of programmatic advertising, there are methods to minimize or eliminate its impact. Here are the key steps business leaders can take to protect both their ad spending and reputation.
Apply powerful ad fraud detection techniques and solutions
Today there are a number of anti-fraud, ad fraud detection, tracking systems and such that apply different types of fraud prevention methods. Such tools may be either a solution or a part of other marketing solutions as an anti-fraud functionality.
However, using all the solutions at once is not a way out. Each advertising business has its own peculiarities, so it is very important to find a personalized strategy that suits your specific processes. When you have a custom ad tech solution to run advertising campaigns, a ready-made anti-fraud solution may not cover you and you’ll need to look for custom options, integrating several different solutions, and so on.
Ad fraud detection technology plays a fundamental role in any fraud risk management strategy. For example, in the case of bots or hijacked devices, the invalid traffic occurs within the first 48 hours after the device has been infected.
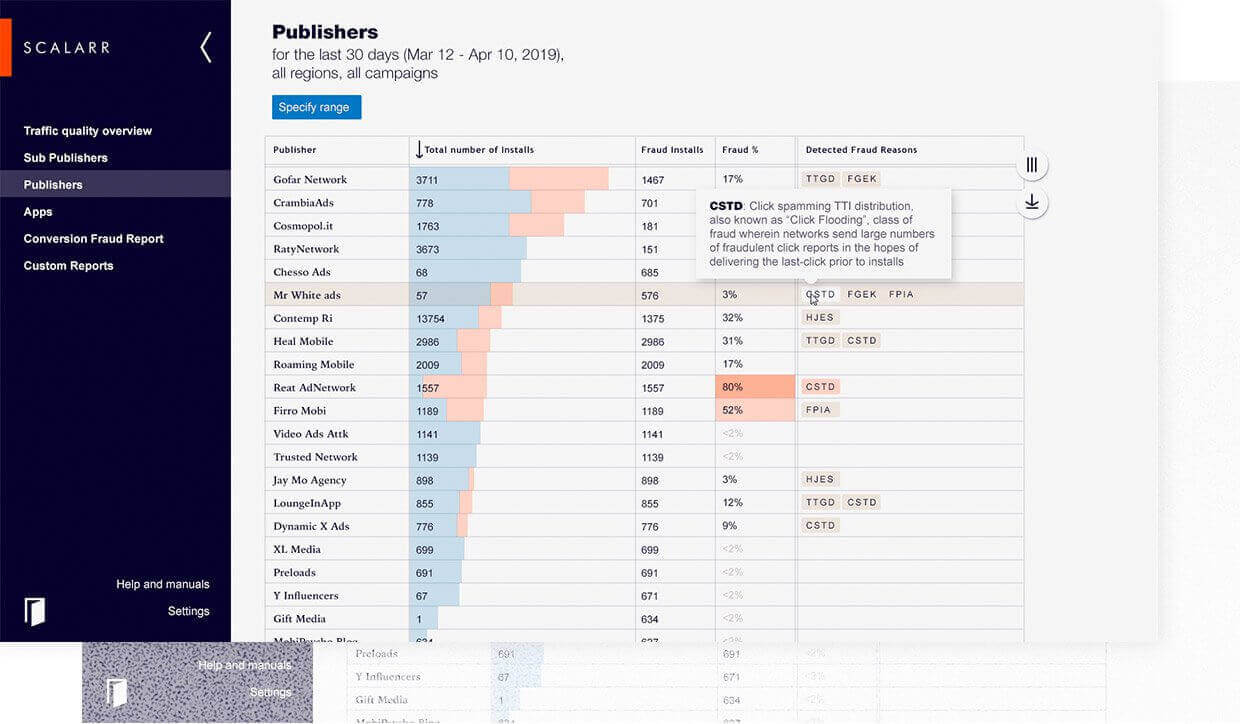
To speed up detection, some providers very often use different AI-based approaches and machine-learning models. For example, Scallar suggests an advanced AI-enabled anti-fraud toolkit for mobile marketers. It applied various machine learning algorithms to automatically analyze hundreds of clicks, installs, and post-install event features to define fraud patterns from huge amounts of data.
Scalarr’s dashboard
Source: scalarr.io
In addition to the above, different ad fraud types require different approaches to ad fraud detection. For example, for:
- general invalid traffic it’s enough to apply industry-wide supplied lists of known bots,fraudulent sites, spiders, data centres and unknown browsers.
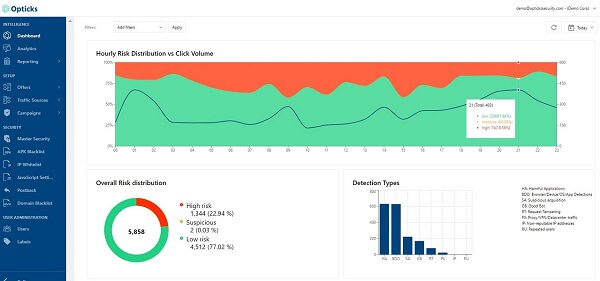
- bots the speed of detection and definite understanding of what is an invalid traffic plays a core role. It’s all because new bots live for 72 hours on average and generate the highest amount of fake impressions within the first 24 hours. Companies usually use the combination of both server-side and client-side signals to detect bots. While server-side modules gather HTTP requests, client-side (in-browser) records and analyzes various behavioral signals.
Example of the modern ad fraud detection solution by Opticks
Source: optickssecurity.com
- website and app fraud require automated algorithms to define potentially fraudulent sites and apps. Data scientists work on analyzing apps and websites by means of a highly accurate, heuristic model that involves different empirical, technical and non-technical data points. For example, for mobile fraud detection it is important to monitor such indicators as device rate, device sensors, limit ad tracking (LAT) identifier, click to install time (CTIT) and others. If the CTIT is under 10 seconds there is a risk of installing hijacking fraud, while CTIT above 24 hours hints at possible click flooding fraud.
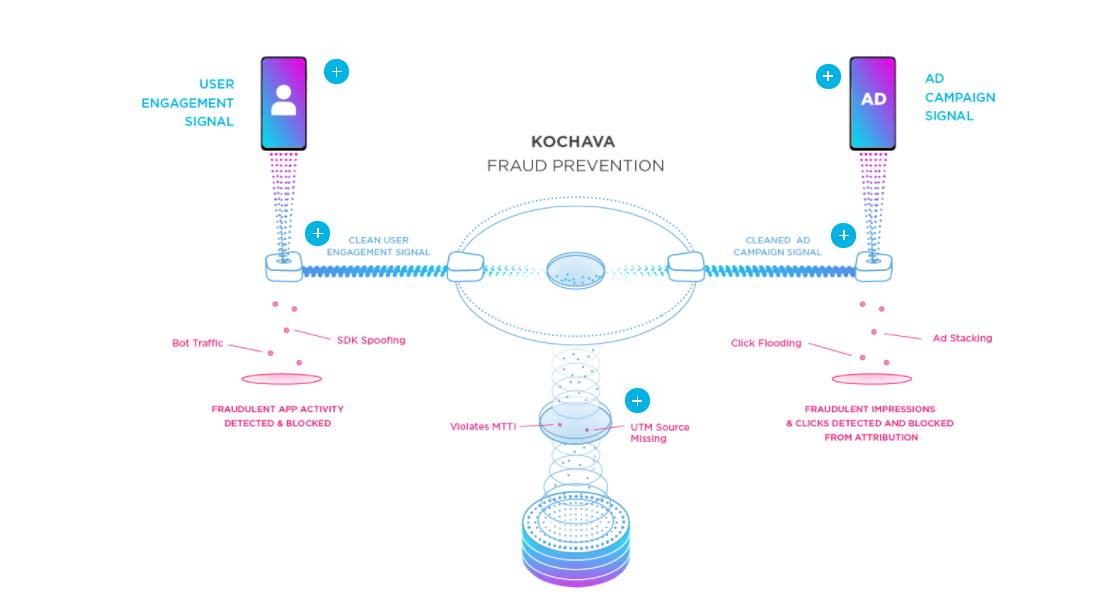
Source: kochava.com
- adware and malware also involving hijacked devices or injected ads, need more sophisticated real-time signal processing within the browser. For this purpose providers apply machine-learning technologies and fraud analysis to define the signatures related to malware and adware-served impressions.
- CTV ad fraud together with using specific anti-fraud systems and instant performance reports require cooperation with certified advertisers and working with trusted publishers. Today, Pixalate is the only anti-fraud vendor accredited by the Media Rating Council for CTV and OTT video impression measurement. Although such companies as MOAT and Double Verify are also developing viewability measurement and safety tools, neither are certified yet. So if you are choosing an anti-fraud system for CTV advertising, check the credibility of the vendor.
Follow the recommendations of companies that investigate fraud
There are a number of industry working groups and organizations like Interactive Advertising Bureau (IAB), Media Rating Council (MRC), Trustworthy Accountability Group (TAG), and others that accreditatate certain solutions and vendors to fight ad fraud.
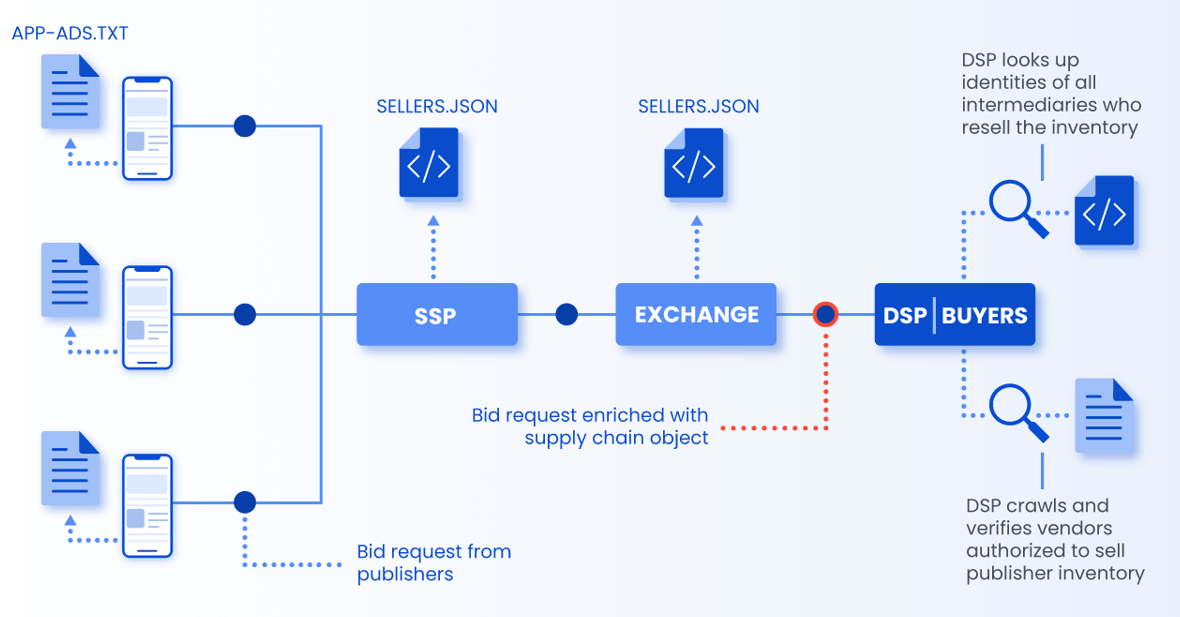
Companies highlighted also regularly release certain industry standards and programs focused on eliminating fraudulent activity in advertising. For example, The IAB Tech Lab has introduced ads.txt which is a text file that publishers can place on their websites to show ad buyers a list of authorized resellers for their ad inventory.
The IAB Tech Lab also constantly releases updates to this standard to keep on eliminating the ad fraud threats. In 2019, they released a new version called app-ads.txt, which was created to support mobile applications, OTT technology, and any other mobile inventory. In 2021 the company introduced the updates to ads.txt and app-ads.txt which provide the ability to model “inventory sharing” on CTV environments.
One more IAB Tech Lab’s standard worth considering is sellers.json that allows checking ad inventory sources, direct publishers and resellers of traffic on ad tech platforms, SSPs, and ad networks.
Example of how app-ads.txt and sellers.json standards work in practice
Source: inmobi.com
The IAB has also developed a more advanced software protocol for filtering fake inventory – RTB 3.0. It has an additional layer of Ads.cert protection that helps detect more sophisticated types of fraud such as ad injections.
Ads.cert provides an additional verification step and can track data passed between buyer and seller at each stage of the programmatic ad supply chain to ensure they are not fraudulent.
These initiatives provide additional transparency and more data that advertisers can use to check if they’re buying fake impressions.
Take care of privacy policy to be compliant and protect the company’s reputation on the ad market
The last but not least important step in ensuring ad fraud protection is brand safety and compliance. It’s important to understand that besides using innovative anti-fraud solutions, all ad tech players should take care of their privacy policy.
Can you imagine that around 22% of apps on the App Store and 9% on Google Play that serve programmatic advertisements didn’t have a privacy policy as of May 2021? This is very significant because there have already been cases when consumer data was violated in terms of different ad fraud schemes.
One such scheme was Matryoshka which impacted at least two million iOS and Android users and acquired personal user information without asking permission. In view of this, taking care of privacy policy and compliance is a necessary screw in your solid fraud risk management strategy.
Build a secure ad tech solution with MindK
Here at MindK, we accumulated large experience in developing software for marketing and advertising. We can help you build powerful and secure ad tech products that can process millions of data points, integrate with ad campaign management tools, and provide the best return on your ad spend.